Why Does Security Compliance Matter?
In today’s world, data is important, and mishandling it can cause big problems. Governments and industries are making stricter rules to protect personal data and business systems. If your business doesn’t follow these rules, you could face fines, lawsuits, and damage to your reputation.
This article will share simple ways to keep your business safe and follow security rules like GDPR, HIPAA, and others. We’ll explain each step clearly and show you how to stay compliant.
What Is Security Compliance?
Security compliance means following rules to protect data and systems. These rules help ensure:
- Confidentiality: Keep sensitive data safe.
- Integrity: Make sure data is correct and hasn’t been tampered with.
- Availability: Ensure systems are running when needed.
In simple terms, compliance is about following the rules to keep your data safe.
Key Security Best Practices For Compliance
1. Understand the Regulatory Landscape
Why It Matters:
You can’t protect what you don’t know. Each rule has its requirements.
Action Steps:
- Know which rules apply to your business (GDPR, HIPAA, etc.).
- Know where your data goes, how it’s stored, and who has access to it.
- Talk to legal or compliance experts to avoid mistakes.
✅ Why this helps: Knowing the rules helps you protect your data better and reduces the risk of audits.
2. Implement Role-Based Access Control (RBAC)
Why It Matters:
Not everyone should have access to all data. Too many people with access increases the risk of breaches.
Action Steps:
- Give access based on what people need to do their jobs.
- Follow the “least privilege” principle—give the minimum access needed.
- Review access levels regularly.
✅ Why this helps: This protects sensitive data and follows privacy rules like GDPR and HIPAA.
3. Maintain Comprehensive Audit Logs
Why It Matters:
Logs show who accessed your systems and what they did. This proves your systems are secure.
Action Steps:
- Keep logs of all activity across your systems.
- Use tools to manage logs and spot unusual activities.
- Keep logs safe from tampering and review them regularly.
✅ Why this helps: Audit logs are essential for investigations and are required in most compliance audits.
4. Encrypt Data In Transit And At Rest
Why It Matters:
Encryption protects data from being stolen or accessed by unauthorized people.
Action Steps:
- Use encryption tools like TLS 1.3 for secure communication.
- Encrypt data stored in your systems.
- Manage encryption keys securely.
✅ Why this helps: Encryption keeps your data private, even if it is intercepted.
5. Conduct Regular Risk Assessments
Why It Matters:
Security risks change over time. What worked last year may not work today.
Action Steps:
- Identify and prioritize the assets you need to protect.
- Look for potential threats and weaknesses.
- Evaluate how likely risks are and their impact.
- Plan actions to reduce these risks.
Risk Score = Likelihood × Impact
✅ Why this helps: Regular assessments are a key part of rules like ISO 27001 and GDPR’s data protection assessments.

6. Train Employees on Security Awareness
Why It Matters:
Most security breaches are caused by human error.
Action Steps:
- Train employees regularly, especially when they join the company.
- Run tests like fake phishing emails to raise awareness.
- Teach employees how to report suspicious activities.
✅ Why this helps: Educated employees help prevent breaches and fulfill training requirements under laws like HIPAA and SOC 2.
7. Create and Test an Incident Response Plan
Why It Matters:
When something goes wrong, how quickly you react is critical. A good plan minimizes damage.
Action Steps:
- Define roles and steps for dealing with security incidents.
- Practice your plan regularly through simulations.
- Review what went well and what didn’t after each incident.
✅ Why this helps: Regulations like PCI-DSS and GDPR require fast and thorough incident response.
8. Keep Software and Systems Updated
Why It Matters:
Old, unpatched software is an easy target for attackers.
Action Steps:
- Set the software to update automatically.
- Use tools to track updates and patches.
- Stay informed about known software weaknesses.
✅ Why this helps: Keeping systems updated removes security holes that can be exploited.
9. Secure Third-Party Vendors
Why It Matters:
Your vendors might have access to your systems, so you need to ensure they are secure too.
Action Steps:
- Assess the security of all third-party vendors.
- Require vendors to have compliance certifications.
- Make sure your contracts with vendors include security clauses.
✅ Why this helps: You are responsible for your vendors’ security, and violations can harm your business.
10. Document Everything
Why It Matters:
If something isn’t documented, it’s as if it never happened—especially during audits.
Action Steps:
- Keep records of policies, procedures, assessments, and security incidents.
- Make sure documents are easy to find and up to date.
- Use version control to track changes to documents.
✅ Why this helps: Good documentation makes audits easier and shows you are committed to security.
FAQs
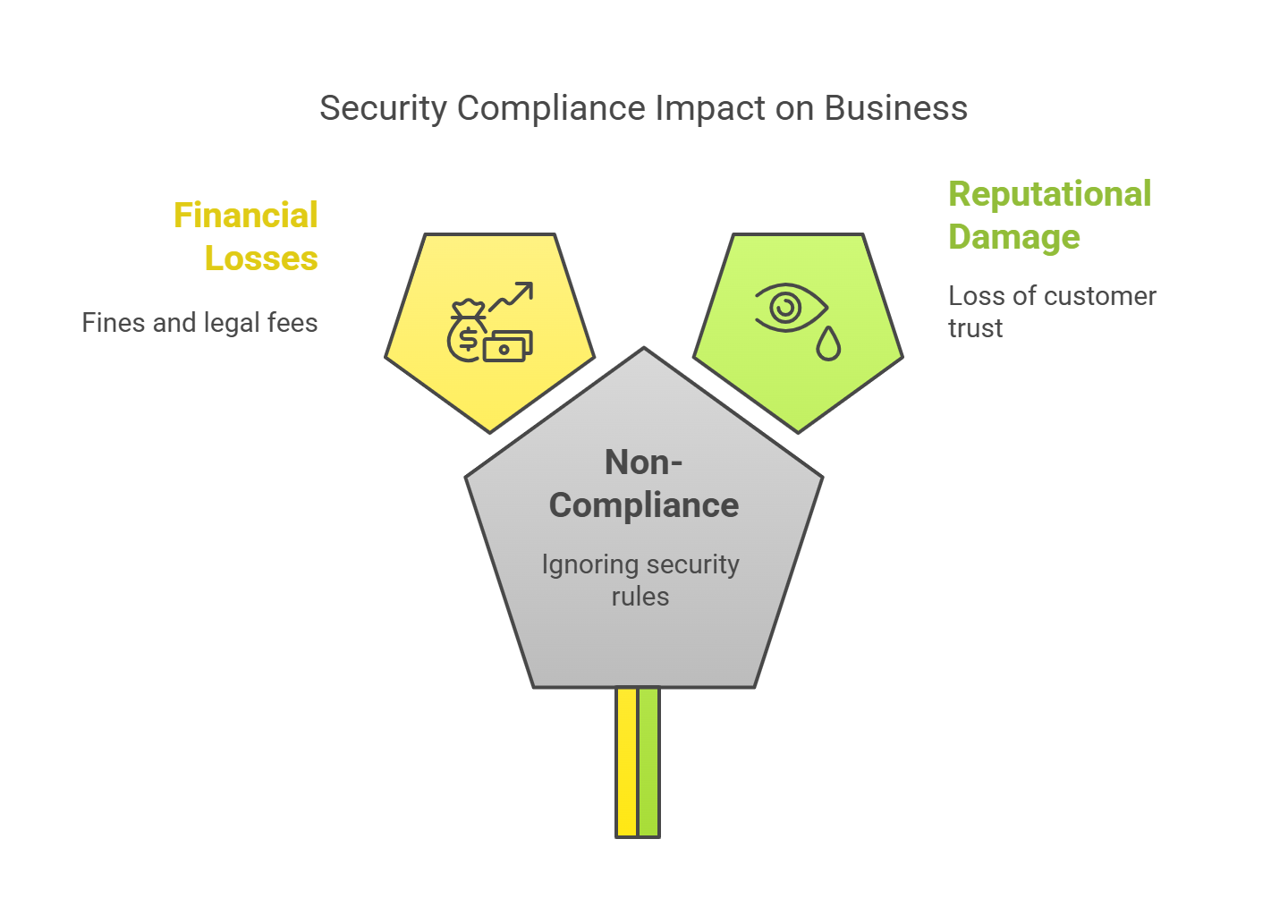
What Happens If My Business Is Not Compliant?
If you don’t comply, you could face:
- Large fines (like GDPR’s €20 million fine).
- Lawsuits and legal trouble.
- Loss of customer trust.
- Service shutdowns.
How Often Should I Perform Security Assessments?
You should assess your security:
- Every 6–12 months.
- When you add a new vendor.
- When a new security threat arises.
Can Small Businesses Be Exempt From Compliance?
No. All businesses that handle certain types of data must follow security rules, even small ones.
Is Compliance The Same As Security?
No, compliance means meeting legal rules, while security is about proactively protecting your data. Both are important for full protection.
Quick Calculation: Risk Impact Score
Here’s a simple way to calculate risk:
Risk Score = Likelihood (1–5) × Impact (1–5)
Example:
- Likelihood of breach = 4 (High)
- Impact = 5 (Severe)
Risk Score = 4 × 5 = 20 (Critical Risk)
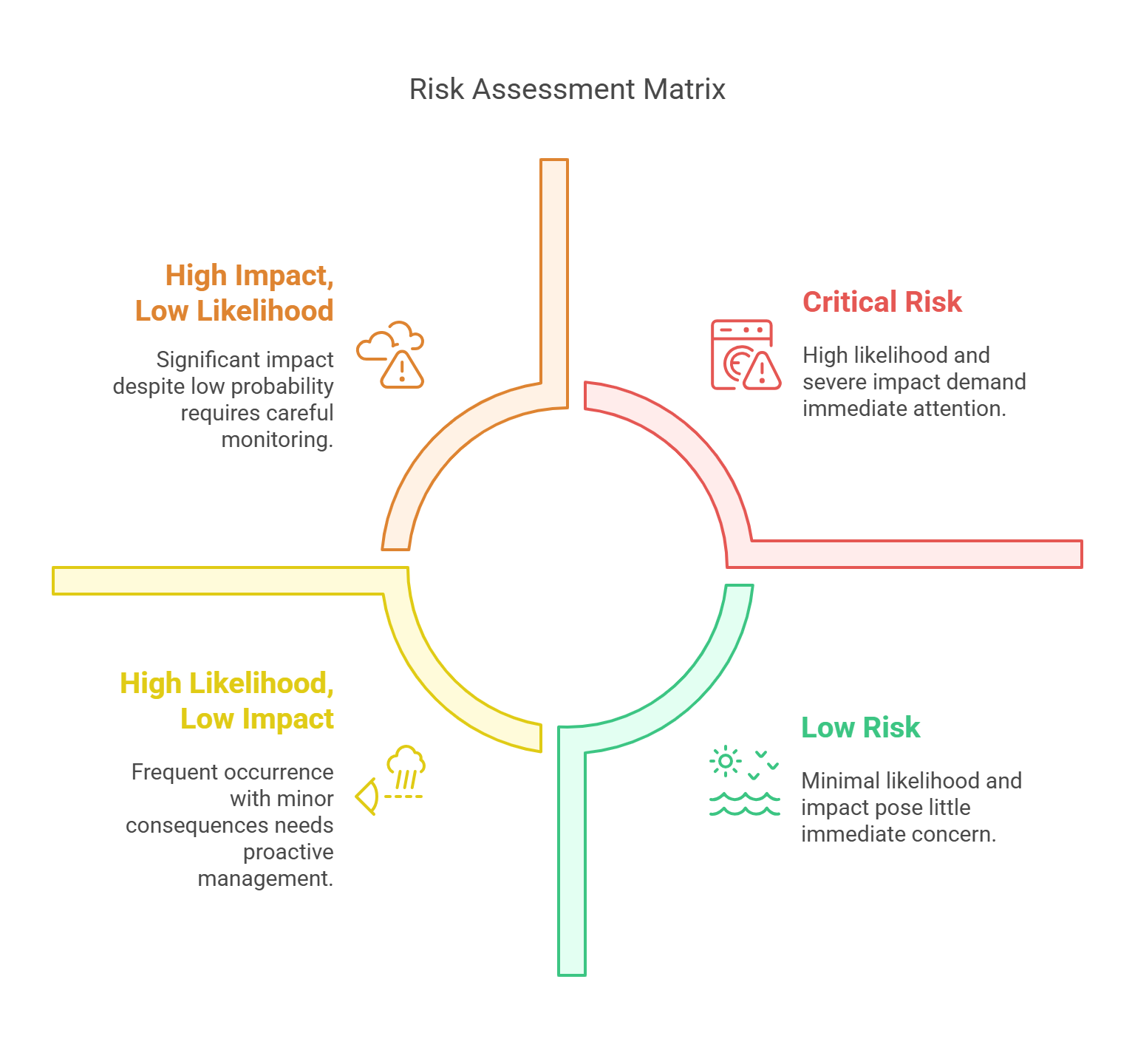
Use this score to focus on high-risk areas during assessments.
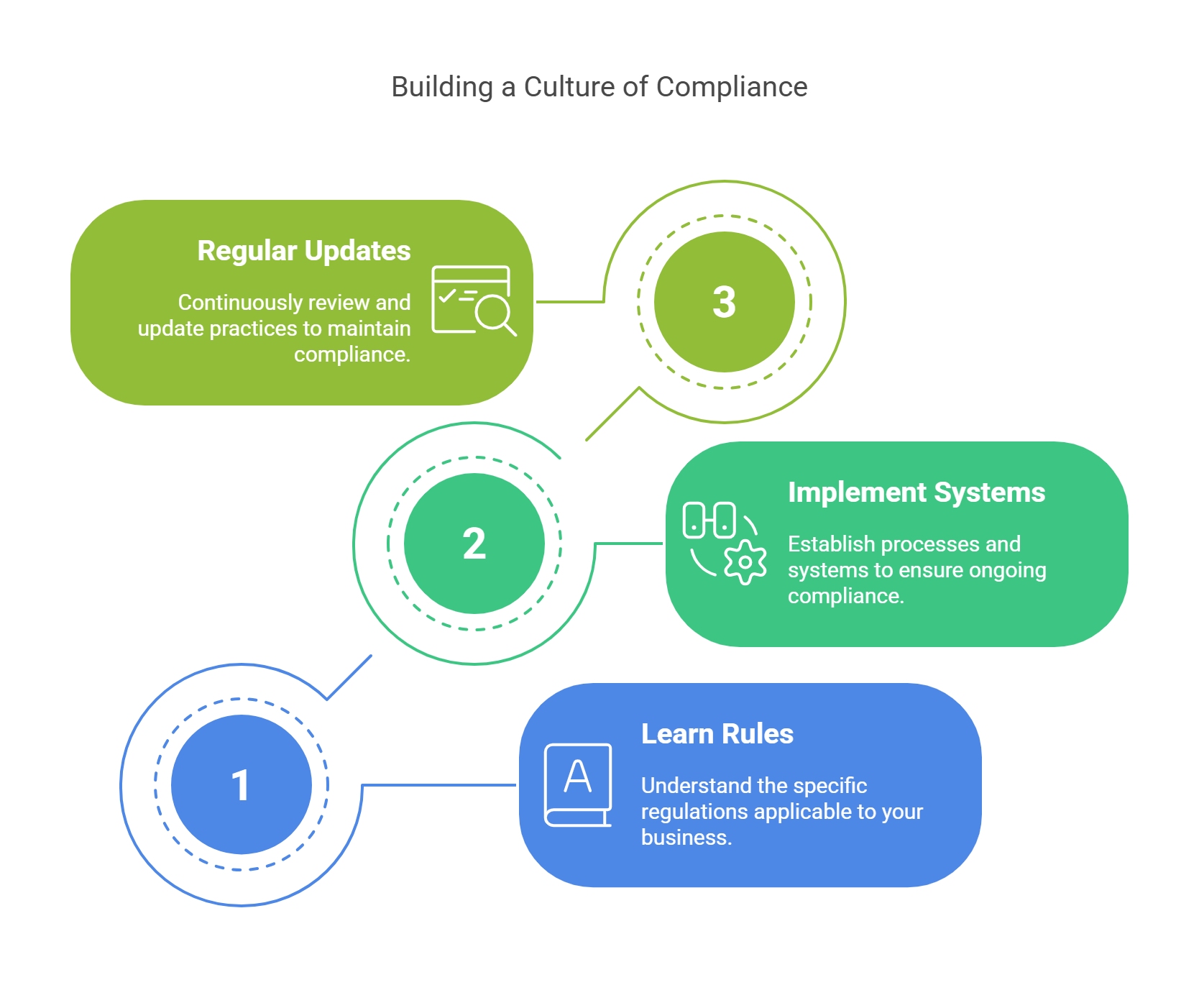
Conclusion: Compliance Is Not a One-Time Event—It’s a Culture
Security compliance isn’t just about checking boxes. It’s about creating a culture of responsibility that protects your business and data.
✅ Start by learning which rules apply to your business.
✅ Then, put systems and processes in place to stay compliant.
✅ Finally, regularly check, improve, and update your practices.
Is your business ready for compliance? Don’t wait for an audit or a breach to act.
Start today by reviewing your practices. Train your team. Improve your security.
Remember, in cybersecurity, being prepared isn’t optional—it’s essential.