Why Is Website Penetration Testing So Important?
Your website is an important part of your business. Cybercriminals are always looking for weak spots. This is where website penetration testing comes in.
Website penetration testing, or web pen testing, is when experts test your website to find its weaknesses before hackers can. This helps you protect data, earn trust, and meet privacy laws.
Let’s examine penetration testing, why it’s important, and how to use it well.
What Is Website Penetration Testing?
Website penetration testing is when ethical hackers simulate cyberattacks on your website to find security flaws.
The goal is simple:
Find weaknesses before attackers do.
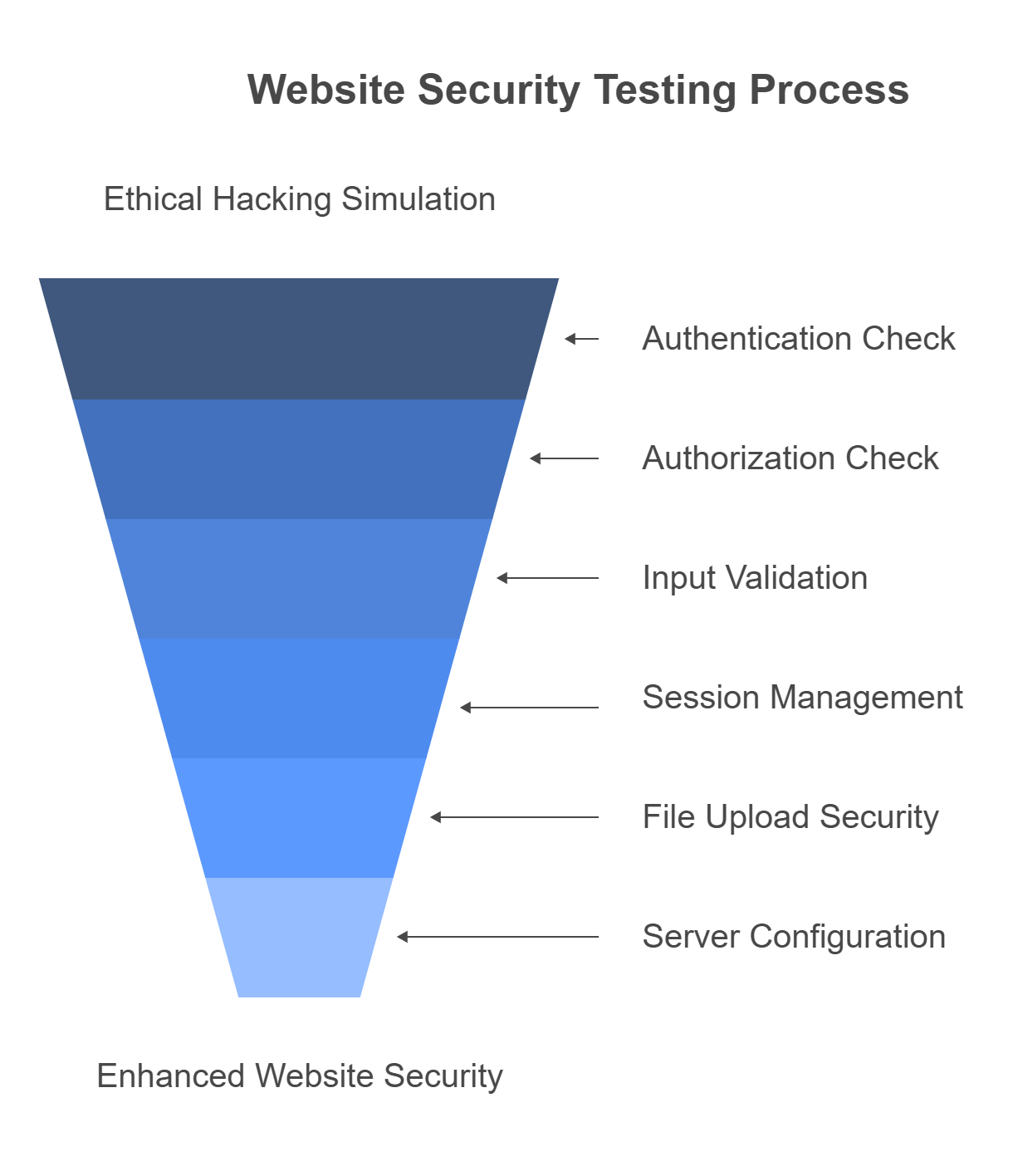
What’s Tested?
- Authentication: Are users properly verified?
- Authorization: Can users access things they shouldn’t?
- Input Validation: Are user inputs checked for security issues?
- Session Management: Are user sessions secure?
- File Uploads: Can harmful files be uploaded?
- Server Configuration: Is your server set up to resist attacks?
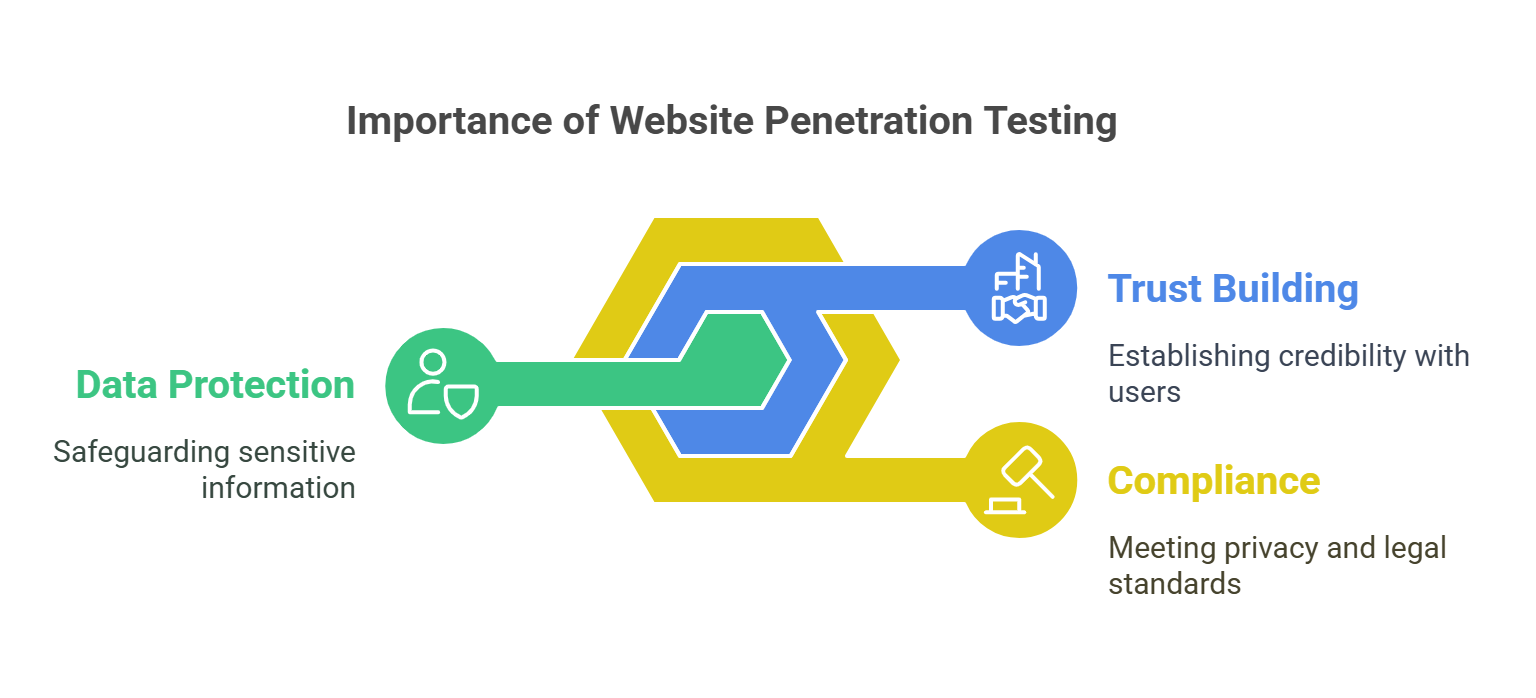
Why Do You Need Website Penetration Testing?
1. Protecting Data And Privacy
A breach can expose sensitive customer data. Penetration testing helps find and fix flaws before attackers can steal data. It also helps you follow privacy laws like GDPR and CCPA.
2. Meeting Legal And Industry Standards
Penetration testing is required by laws and industry standards like PCI-DSS and ISO 27001. If you don’t test regularly, you may face penalties.
3. Keeping Your Brand Safe
A breach can damage your brand’s reputation. Pen testing helps protect your website from attacks that could harm your public image.
4. Saving Money
Cyberattacks can be costly. A breach can lead to lost customers, legal fees, and fines. Penetration testing helps avoid these costs by finding problems early.
Types of Website Penetration Testing
1. Black Box Testing
The tester has no prior knowledge of the system. This simulates an attack by an external hacker.
- Pros: Most realistic.
- Cons: May miss internal flaws.
2. White Box Testing
The tester has full access to the system, including the source code and architecture.
- Pros: Very thorough.
- Cons: Requires access to code and documentation.
3. Gray Box Testing
The tester has some knowledge, like login credentials or access to parts of the system. This simulates an insider threat.
- Pros: Balanced approach.
- Cons: May miss vulnerabilities that external hackers could find.
Key Areas Tested During Penetration Testing
🔐 Authentication & Authorization
- Are users correctly verified before accessing sensitive data?
- Can attackers escalate privileges to get unauthorized access?
🧱 Input Validation & Injection Flaws
- Are all user inputs properly checked?
- Can attackers inject malicious code (e.g., SQL injection or cross-site scripting)?
🕸️ Session Management
- Are session IDs hard to guess?
- Do sessions expire after inactivity?
📂 File Upload & Download Security
- Can malicious files be uploaded to the website?
- Are file types restricted?
📡 Server Configuration & Error Handling
- Do error messages reveal too much information about the server?
- Is the server up to date with security patches?
The Step-By-Step Website Penetration Testing Process
1. Planning & Reconnaissance
Define the scope and goals of the test. Collect information about the target using tools like WHOIS, Google Dorking, and Shodan.
2. Scanning & Vulnerability Assessment
Use automated tools to scan for common vulnerabilities.
3. Exploitation
Attempt to exploit the weaknesses in a controlled way, simulating a real attack.
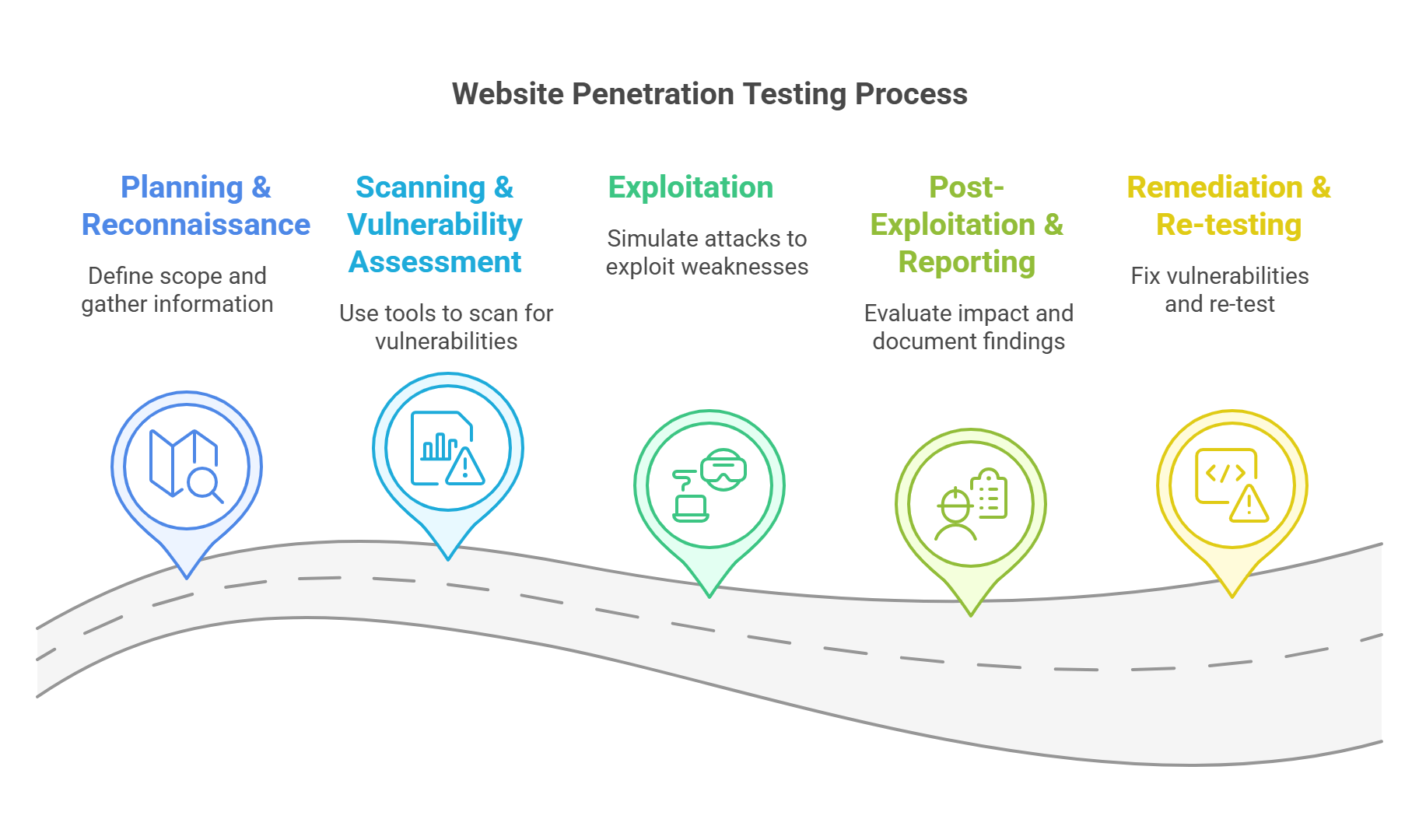
4. Post-Exploitation & Reporting
Evaluate the impact of the exploit. Document the findings and provide proof of concepts (PoCs) and recommendations for fixing the weaknesses.
5. Remediation & Re-testing
Once vulnerabilities are fixed, re-test the system to ensure the issues are resolved.
Tools Used In Website Penetration Testing
| Tool Name | Purpose |
|---|---|
| Burp Suite | Web vulnerability scanner |
| OWASP ZAP | Open-source security scanner |
| Nmap | Network mapping and port scanning |
| Nikto | Web server scanner |
| Metasploit | Exploitation framework |
| Dirb | Directory brute-forcing |
How Often Should You Perform Website Penetration Testing?
The frequency of testing depends on the sensitivity of your data and website changes. Here’s a good rule of thumb:
- Annually for smaller websites.
- Every 6 months, for businesses that handle sensitive data.
- After major updates or new integrations.
Common Vulnerabilities Found in Web Pen Tests
- SQL Injection (SQLi)
- Cross-Site Scripting (XSS)
- Cross-Site Request Forgery (CSRF)
- Broken Authentication
- Sensitive Data Exposure
- Security Misconfiguration
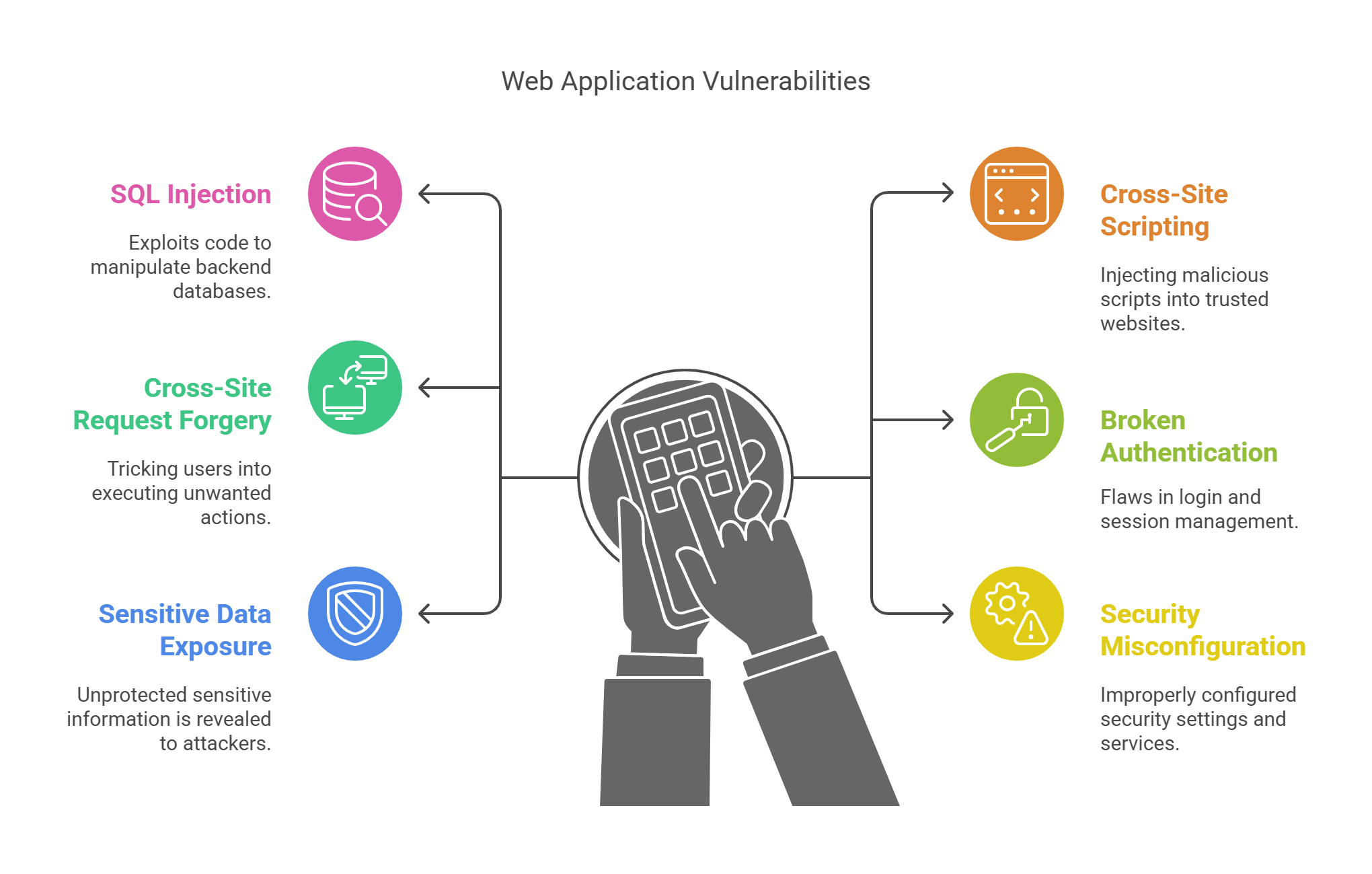
These vulnerabilities are in the OWASP Top 10, a list every developer should follow to secure their web applications.
FAQs
What’s The Difference Between Pen Testing and Vulnerability Scanning?
- Vulnerability scanning automatically finds potential weaknesses.
- Penetration testing goes further by exploiting these weaknesses to understand the real risks.
Do I Need A Certified Ethical Hacker For Pen Testing?
While it’s not required, having a certified professional (e.g., CEH, OSCP) ensures the testing is done correctly.
Can Pen Testing Damage My Website?
If done properly, no. Ethical hackers use controlled methods to avoid disrupting your site.
How Much Does Website Penetration Testing Cost?
Pen testing costs can range from $500 to $15,000+, depending on the complexity of your website.
| Item | Estimate |
|---|---|
| Basic Website Test | $500 – $2,000 |
| E-commerce Platform | $3,000 – $10,000 |
| Large-Scale Application | $10,000+ |
Given that the average cost of a data breach is over $4.45 million, pen testing is an affordable way to protect your business.
Best Practices For Effective Penetration Testing
- Set clear goals for testing.
- Use certified ethical hackers for better results.
- Prioritize vulnerabilities based on their business impact.
- Re-test after fixes.
Final Thoughts: Secure Today, Survive Tomorrow
Penetration testing is a crucial tool for businesses of all sizes. It helps you stay ahead of cybercriminals, protect sensitive data, and maintain your brand’s reputation.
Start testing today to build a stronger, safer website tomorrow.
📌 Key Takeaways
- Pen testing simulates cyberattacks to find weaknesses.
- It helps protect data, ensure compliance, and build trust with customers.
- Use tools like Burp Suite and Nmap to conduct effective tests.
- Regular testing helps reduce the risk of costly cyberattacks.